
We say it often, “Security is a Journey. Not a Destination”. You are never done when it comes to protecting your enterprise environment. Ongoing security assessments are imperative to help identify new/existing vulnerabilities and develop a plan for remediation. Penetration testing, or pen testing, is the simulation of real-world attacks in order to test an organization’s detection and response capabilities. While some might consider pen tests as just a vulnerability scan meant to check the box on a compliance requirement, the exercise should actually be much more.

Use EDR-grade detection to achieve unparalleled visibility into processes and scripts.
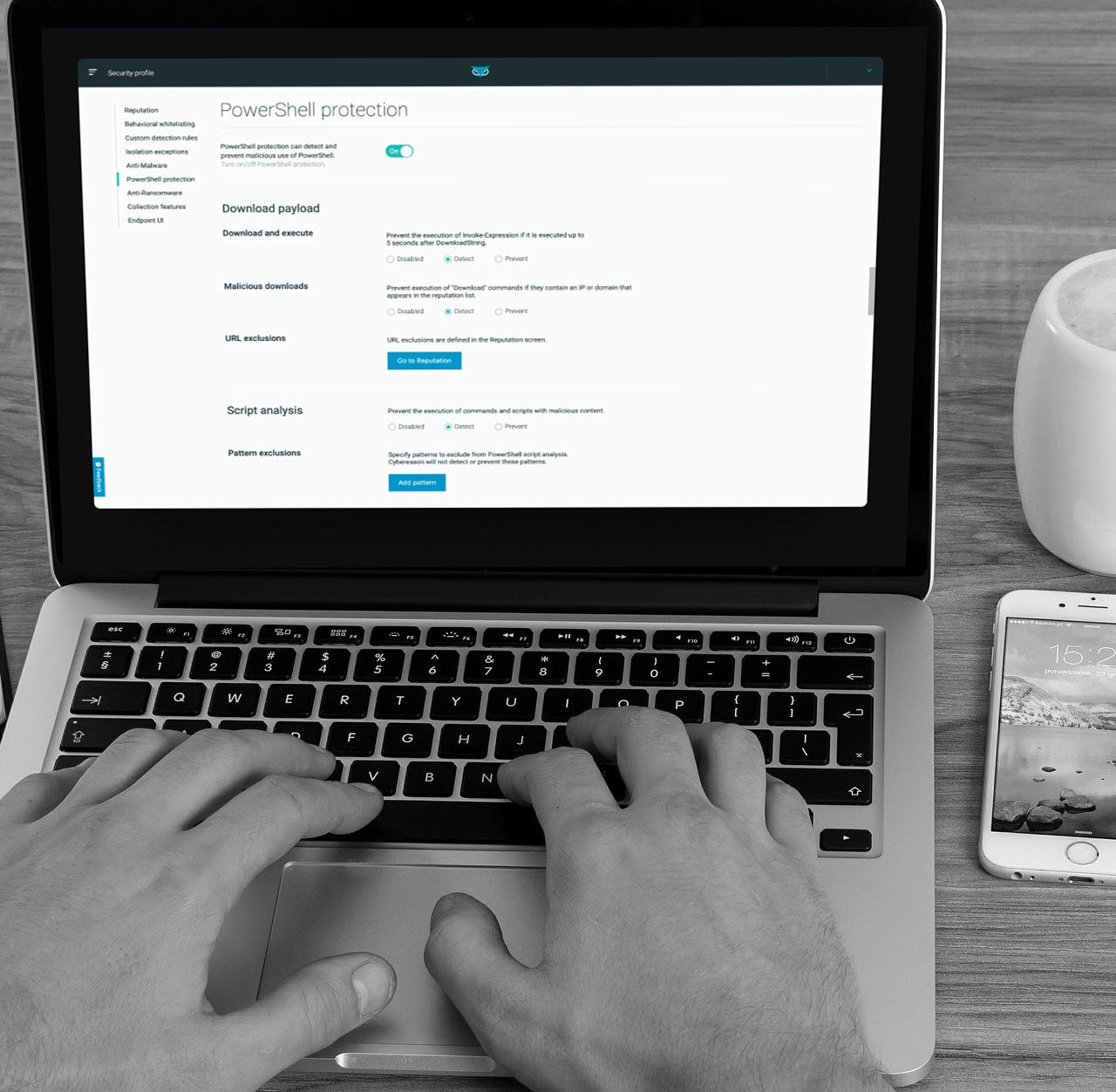
First in the market to block malicious .Net execution, Cybereason continues to develop new forms of visibility into PowerShell scripts, .Net abuse, Macro scripts, and more.
The result is less risk from elusive attacks getting through, and lower investigation workload.

Cybereason Prevention offers multi-layered prevention with minimal impact on performance and needed resources - and without needing to deploy multiple agents.
Deploy Cybereason Prevention in as little as 24 hours with minimal organizational impact, and start preventing attacks the same day.
Harden endpoints with device control, personal firewall, and full disk encryption.